When a malware succeeds to gather over $200 million in just two years, it deserves the title of the most vicious one so far. Ransomware did that, and the number is still ascending. Statistics show that a vast majority of these victims are based in the US. The UK follows in numbers, while the western European countries fill the rest of the list. The attacks are well-planned and targeted to both private and corporate users. More than half of US victims decide to pay the ransom which averages around $400.
The main reason for ransomware’s success lays in its non-removable nature, once it’s active. Some security companies have succeeded to crack some of the keys which can disarm it. Unfortunately, that’s not nearly enough codes comparing to the number of new versions of ransomware. In order to show you the seriousness of the issue, we have found some examples of people and companies who had misfortune with ransomware.
Case #1
A regular user – probable cause of her infection was often use of torrent sharing websites without any protection. It’s hard to determine how long she had ransomware on her hard drive. Once engaged the ransomware displayed a clear message, including its name, developer, details of encryption and steps to take to disarm it.
Since all photos and videos of this user were on her hard drive, there was no other option but to pay the ransom. Hacker demanded payment in Bitcoins, one actually, which at that time was around $350. The deadline – three days. The woman did everything and paid the ransom. Lucky* for her, the data was unlocked as promised.

* There are a few problems with this method. First of all, how can you trust someone who abducted your personal data in the first place? What guarantee do you have that hackers won’t ask for more money? Even if they are honest, provided step-by-step guide takes some serious computer knowledge. If you are not savvy, you can forget about unlocking your data.
Case #2
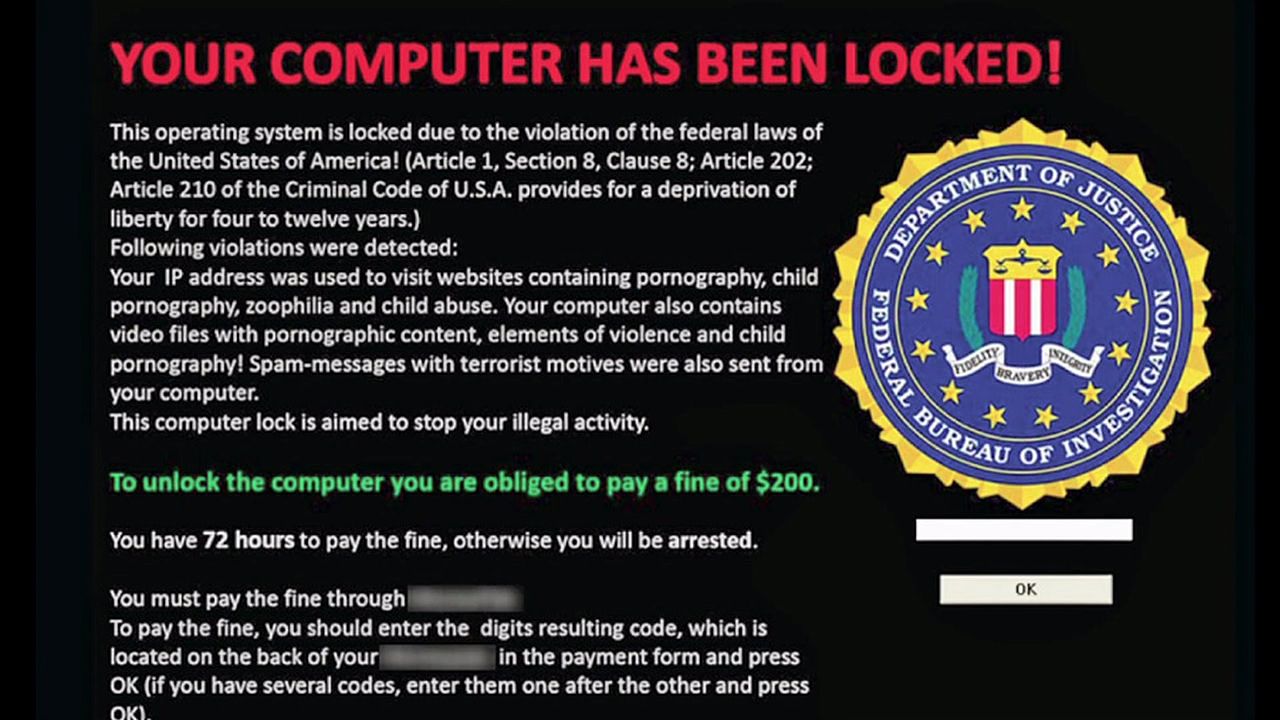
Another typical user – but with poor PC skills. The man was confused when he received a message on his screen coming directly from the FBI. This is a common ransomware trick. The fear of authority increases the chances of success. Everything, except the FBI part, was the same like in the first case.
Since he didn’t know how to use Tor, Onion, VPNs, etc. the man asked for the help of the experts. Even though he was advised not to pay, he decided to go through with it.
IT experts have followed the instructions but were deceived more than once. First, they had problems with Bitcoin purchase. Then there was a risk of credit card number theft on one of the websites. Lastly, the transaction took longer than expected, the money was through, but the encryption remained on the PC. Another payment had to be submitted, and the man decided to forget about his data locked on the computer.
Case #3
A small law firm was a victim of ransomware. The infection came from a single PC which had an outdated antivirus software. Every computer in the office was on the same network, so everything happened quickly. More than a half of computers were infected in a day. With so many important files and documents, the owners thought they have to pay a ransom which was in total around 10k US dollars.
Thanks to a good service of the IT company in charge of maintenance, the ransom was evaded. Their service package included cloud backup at the end of every day. With all the data available online they managed to cut their losses and to get back in business immediately.

Case #4
One more case of corporate attack. In this case, there was the lot more at stake since the company has over 100 employees. The cause of the infection was a corrupted USB. “Patient-zero” had USB scanner turned off, and that’s how the infection got inside in the first place.
Luckily, once the infection was noticed on two PCs, they were cut from the network. Other PCs were cleaned, using professional antivirus software. The price for decryption was 2 Bitcoins per machine. Their luck hasn’t abandoned them, and after the transaction, they did get their keys and successfully unlocked the computers.

With malware so serious, the users have to think ahead and to protect themselves from the criminals. As you can see from these examples, one’s with regular backup and up-to-date antivirus software managed to evade the damage.
ShieldApps Ransomware Defender blacklists every known ransomware, so even if you do pick it up while surfing, downloading, opening a spam email, you’ll be notified about it. The threat will be handled properly and contained. Backup can help you no doubt about it. But, you’ll have to reinstall your system in order to regain normal function of your PC. With professional, and proven ransomware solution you can stay calm and safe at all times.

